tech news
01 Media keeps a finger on the pulse of the latest and greatest in tech trends; technology news coming from large corporations and startups around the world.
What Are Data Feed Solutions?
If you are new to the world of gambling and bet placing you might have a few questions unanswered, to say the least. Since the legalization of online gambling in 1994, the industry has evolved enormously and can offer some amazing insights to all those who are willing to test their luck.
By BetConstruct5 years ago in 01
Technical Advantage Of 2020
It is interesting to read that many colleges and universities have decided to switch from teaching on campus to a distance learning model. Faculties on campus are not necessarily the best teachers, but what is striking is that these faculties must use technology to conform to their respective institutions "decision to use it as a form of social distancing to improve teaching. The most likely outcome is that colleges and universities will be vigilant in helping teachers learn how to use teaching technology and the tools available to help students succeed in their courses.
By Sita Baral5 years ago in 01
How Technology Is Changing Disasters
Technological disasters such as the BP Deepwater Horizon oil spill, chemical spills, and radiation leaks are stressful. Examples of technological disasters In addition to the oil spill and the radiation leak, examples of technological disasters include cases such as the Fukushima Daiichi nuclear power plant in Japan and previous accidents such as Chernobyl and Three Mile Island. Fires and explosions, such as a fire at a nightclub in Warwick, Rhode Island caused by a pyrotechnics failure, are also examples of technological disasters.
By Sita Baral5 years ago in 01
Is It Illegal To Use Vpn
Other countries that do not have the technology to block VPNs have passed laws banning VPN services not registered with the government. The following countries have not only passed laws imposing official restrictions on VPNs, but also in other alarming ways at internet freedom. If legislators in these countries continue on their current course, citizens could face legal consequences for the use of VPNs and other online data protection services.
By Sita Baral5 years ago in 01
Building the trust up with Privacy Marketing Out of concerns about data privacy and brand security,
Building the trust up with Privacy Marketing Out of concerns about data privacy and brand security, marketers today are looking for ways to reach their audiences and win the trust of customers. This is correct because, during the COVID-19 pandemic, data privacy has become the most critical part of modern marketing practices. why? According to a survey, 85% of consumers said they want more companies to trust their data. And 83% of consumers want more control over their data. This means that customer trust and data privacy must be the top priority of marketers, and there is no way to avoid the need to re-evaluate data privacy policies. Obviously, winning and maintaining customer trust by protecting customer data is critical to the company's competitiveness and continued success. But how does the company start to do this? Here are few ways marketers can build customer trust and gain audiences: Building trust to protect customer privacy: To transform customer trust into a competitive advantage, you must first establish trust by protecting customer information and privacy. Another aspect of gaining customer trust is to establish a leading position in privacy and security. Let’s take a closer look at the steps the company takes to protect customer information. Communicate surely and completely. As a part of this process, train clients on the way to achieve services and products via cybersecurity exceptional practices. Two brands, Apple and Mozilla, have carried out this and hooked up themselves as facts champions. Ensure you manage privacy through design Design privacy is a key element in building customer trust because it puts privacy and data protection at the center of your entire business operations. The privacy design framework requires data and user privacy to be considered during the entire product development process. The organization must obtain consumer data that explains its benefits and agrees to use. If available, companies should use these additional data points to provide more specific user information, thereby improving the quality of advertising. Proactive transparency: To gain a competitive advantage in data privacy, transparency is the key to gaining and maintaining customer trust. Don't wait for laws and regulations to reveal the truth about how you process and store data. Instead, use transparency as a way to win customer loyalty. Do not rely on your privacy policy for all communication for you, thus becoming passive in the way you communicate data practices. Let customers fully understand the data you have about them, the source of the data, how it was collected, and how to use the data in a user-friendly way. Regarding the issue of transparency, marketers can provide readers with more information about how and why they became a target. Think about "Why do I see this ad" on YouTube. Similarly, resources that educate readers about the technology behind advertising can help reduce the fear caused by the uncertainty that viewers experience. Once again, transparency leads to trust. As consumers choose not to share data and consume content in cookie-free environments such as mobile devices, audio, and connected TVs, marketers need to be more creative in their messaging and delivery to ensure they provide their audience with what they want. participate. Many brands and agencies have to stop and rethink how they will advertise in the new environment. The pandemic has made the situation more complicated, and identity resolution will become an increasingly important priority. Hackers, consumer data privacy laws, and related technologies are all constantly evolving. Therefore, the company's data privacy plan must also be adjusted. If marketers regularly evaluate their methods of handling customer data, they can easily pass regulatory requirements. Today’s consumers are more aware and aware of what they want, which means that marketers must first respect their customers’ expectations before trying to gain their trust. Generally speaking, both consumers and regulators need to trust the companies with which they do business to process their data. Due to recent events, they are even willing to accept more regulations to achieve this goal. Companies can build trust with these consumers by being transparent, investing in appropriate data security policies, and maintaining consistency of data privacy policies throughout the organization.
By Brandsandu5 years ago in 01
What Is Facebook
Users can follow content posted by other users without having to make friends with them. You can block external search engines from linking to your profile, but Facebook users are still easily searchable through Facebook's own search engine. The Discovery tab allows bots to be found by activating specific brand QR codes that can be scanned to direct users to specific bots.
By Sita Baral5 years ago in 01
In Which Script Is Windows Based On
For example, the Microsoft Script Debugger allows you to execute one statement after another. If there is a problem with a script, the debugger can help you locate its location. Users can also install another scripting engine to create scripts in other languages, such as PerlScript.
By Thomos James5 years ago in 01
Is Android Based On linus Script
Android is based on a mobile version of the Linux operating system with Android as its core. It is an operating system optimized for mobile devices and others speak of it as a middleware application framework that enables developers to develop applications using the Java programming language.
By Thomos James5 years ago in 01
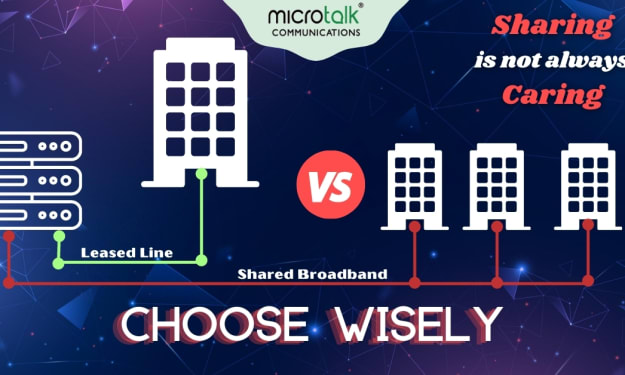
Internet Leased Line VS Broadband Connection
It needs no rocket science knowledge to understand that seamless internet connectivity is the most important criteria for business success. Having a high-performance internet connection helps in setting up highly productive and enhanced collaboration, efficient operation, and increase business productivity. While searching for fast and hustle free internet solution, businesses usually come across two most common networking solutions. They being ILL – Internet Leased Line and Broadband Connection. In a multidimensional office where business owners have to deal with converged applications, there is a need for an ILL connection over the traditional broadband connection. With ILL one gets a one-stop solution for most common problems like downtime, pooling of resources, sharing bandwidth, and low speed.
By Microtalk Communications5 years ago in 01
iPhone 12 Mini Review
In 2020 after several years of following the industry trend for large screen pocket busting phones, Apple made an interesting decision and bucked the trend. The iPhone SE 2nd Generation, released in April 2020, saw the company return to the small form factor for which it was once known. This phone has a 2.65" wide, 5.45" tall body with a 4.7" screen. Weighing in at just 148 grams it was easy to hold and fit nicely in the pocket.
By Paul Douglas5 years ago in 01
What is Web Scraping? A Guide on How to Collect Data From a Website
As we know, a huge amount of data is always a better option for the initial start. There are times when doing work, you require larger amount of data in a short period. However, the amount of data will depend on aims for fetching the data. More data will make you proud. Hence, for more precision and efficiency, you will need an ultimate solution for data collection, which you can easily expand as per the requirement.
By rebeka cox5 years ago in 01
Is Ethernet Faster Than Wifi
New wireless AC routers have data transfer speeds up to three times faster than older B & G wireless models, and they have dual bands, so you have free channels available for older wireless devices. New Wi-Fi 6 routers have data transmission speeds up to 3x faster than traditional Wi-Fi 5 solutions. They also offer dual band, so you get free channels that older wireless devices can access.
By Sita Baral5 years ago in 01